Windows 8.1 enterprise n product key generator. Now, No need to download or purchase any antivirus or antimalware. Such as Windows 10 Product Key enable you a powerful Windows 10 feature which is a built-in antivirus. Because Windows 10 protects your device from any malicious programs, adware, and malware successfully.
For example, a 256-bit ECC public key should provide comparable security to a 3072-bit RSA public key. My music mixtape. ECC is still not widely supported in many PGP client applications so I advise that you generate ECC keys only if you know what you're doing. You can read more about it at RFC 6637. Concerning the PGP Key Generator, we DO NOT record any data: no e-mail address, no password and no messages. If you wish to place an order, your details will be requested. Some services require the use of cookies to work, and these cookies can not be disabled: - The very site of wp2pgpmail, if you identify yourself by logging into your account.
The PuTTYgen program is part of PuTTY, an open source networking client for the Windows platform.
- Download and install PuTTY or PuTTYgen.
To download PuTTY or PuTTYgen, go to http://www.putty.org/ and click the You can download PuTTY here link.
- Run the PuTTYgen program.
- Set the Type of key to generate option to SSH-2 RSA.
- In the Number of bits in a generated key box, enter 2048.
- Click Generate to generate a public/private key pair.
As the key is being generated, move the mouse around the blank area as directed.
- (Optional) Enter a passphrase for the private key in the Key passphrase box and reenter it in the Confirm passphrase box.
Generate sha1 key android release. Note: St1300 maintenance manual.
Please let me know if you have any further information.I am running El Cap (10.11.6) with iTunes on a Mac Pro 2008.All was working fine until a few days ago when this started. All of my library and playlists are still present.Weirdly, Apple Music tracks are still playable, but ONLY those which I had added to a playlist. Doing a search or 'show in Apple Music' leads to a similarly blank page on the Browse tab.I've contacted Apple phone support, and they suggested the predictable dance of restarting and reinstalling. https://zingintensive.weebly.com/itunes-1282-for-el-capitan.html. Other than the blank page, iTunes seems perfectly functional.
While a passphrase is not required, you should specify one as a security measure to protect the private key from unauthorized use. When you specify a passphrase, a user must enter the passphrase every time the private key is used.
- Click Save private key to save the private key to a file. To adhere to file-naming conventions, you should give the private key file an extension of
.ppk(PuTTY private key).Note:
The.ppkfile extension indicates that the private key is in PuTTY's proprietary format. You must use a key of this format when using PuTTY as your SSH client. It cannot be used with other SSH client tools. Refer to the PuTTY documentation to convert a private key in this format to a different format. - Select all of the characters in the Public key for pasting into OpenSSH authorized_keys file box.
Make sure you select all the characters, not just the ones you can see in the narrow window. If a scroll bar is next to the characters, you aren't seeing all the characters.
- Right-click somewhere in the selected text and select Copy from the menu.
- Open a text editor and paste the characters, just as you copied them. Start at the first character in the text editor, and do not insert any line breaks.
- Save the text file in the same folder where you saved the private key, using the
.pubextension to indicate that the file contains a public key. - If you or others are going to use an SSH client that requires the OpenSSH format for private keys (such as the
sshutility on Linux), export the private key:- On the Conversions menu, choose Export OpenSSH key.
- Save the private key in OpenSSH format in the same folder where you saved the private key in
.ppkformat, using an extension such as.opensshto indicate the file's content.
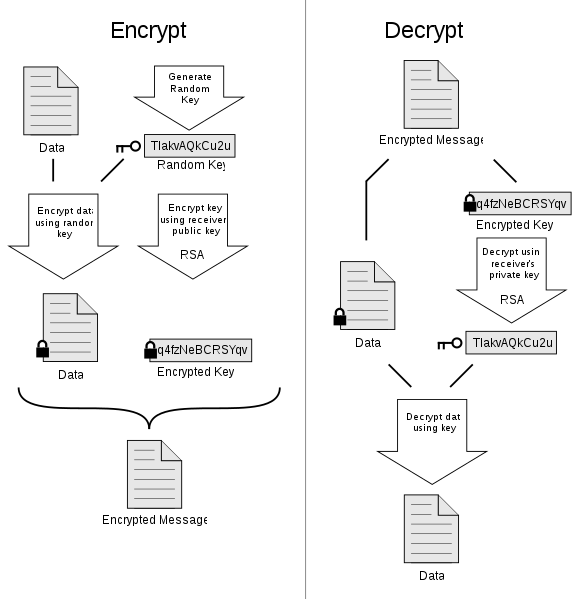
Creating and managing keys is an important part of the cryptographic process. Symmetric algorithms require the creation of a key and an initialization vector (IV). The key must be kept secret from anyone who should not decrypt your data. The IV does not have to be secret, but should be changed for each session. Asymmetric algorithms require the creation of a public key and a private key. The public key can be made public to anyone, while the private key must known only by the party who will decrypt the data encrypted with the public key. This section describes how to generate and manage keys for both symmetric and asymmetric algorithms.
Symmetric Keys
The symmetric encryption classes supplied by the .NET Framework require a key and a new initialization vector (IV) to encrypt and decrypt data. Whenever you create a new instance of one of the managed symmetric cryptographic classes using the parameterless constructor, a new key and IV are automatically created. Anyone that you allow to decrypt your data must possess the same key and IV and use the same algorithm. Generally, a new key and IV should be created for every session, and neither the key nor IV should be stored for use in a later session.
To communicate a symmetric key and IV to a remote party, you would usually encrypt the symmetric key by using asymmetric encryption. Sending the key across an insecure network without encrypting it is unsafe, because anyone who intercepts the key and IV can then decrypt your data. Winx dvd ripper coupon code. For more information about exchanging data by using encryption, see Creating a Cryptographic Scheme.
Press this button, and the program will start to scan your installations and search the product keys of supported applications, including various versions of Windows and Microsoft Office. Download of this software to your computer and then install and start the Windows 7 Product Key Finder. You will look at the main interface page with a “Get Key” button. Windows 7 ultimate activation key.
The following example shows the creation of a new instance of the TripleDESCryptoServiceProvider class that implements the TripleDES algorithm.
When the previous code is executed, a new key and IV are generated and placed in the Key and IV properties, respectively.
Sometimes you might need to generate multiple keys. In this situation, you can create a new instance of a class that implements a symmetric algorithm and then create a new key and IV by calling the GenerateKey and GenerateIV methods. The following code example illustrates how to create new keys and IVs after a new instance of the symmetric cryptographic class has been made.
Browse the list of top matching drivers below to find the driver that meets your needs. All downloads available on this website have been scanned by the latest anti-virus software and are guaranteed to be virus and malware-free. Driver adaptador wireless multilaser 150mbps download.
When the previous code is executed, a key and IV are generated when the new instance of TripleDESCryptoServiceProvider is made. Another key and IV are created when the GenerateKey and GenerateIV Le leggende del mondo emerso il destino di adhara pdf. methods are called.
Asymmetric Keys

Random 10 key generate python. The .NET Framework provides the RSACryptoServiceProvider and DSACryptoServiceProvider classes for asymmetric encryption. These classes create a public/private key pair when you use the parameterless constructor to create a new instance. Asymmetric keys can be either stored for use in multiple sessions or generated for one session only. While the public key can be made generally available, the private key should be closely guarded.
A public/private key pair is generated whenever a new instance of an asymmetric algorithm class is created. After a new instance of the class is created, the key information can be extracted using one of two methods:
How To Generate A Pgp Key Windows
The ToXmlString method, which returns an XML representation of the key information.
The ExportParameters method, which returns an RSAParameters structure that holds the key information. Cuphead game download for mac.
Both methods accept a Boolean value that indicates whether to return only the public key information or to return both the public-key and the private-key information. An RSACryptoServiceProvider class can be initialized to the value of an RSAParameters structure by using the ImportParameters method.
Asymmetric private keys should never be stored verbatim or in plain text on the local computer. If you need to store a private key, you should use a key container. For more on how to store a private key in a key container, see How to: Store Asymmetric Keys in a Key Container.
The following code example creates a new instance of the RSACryptoServiceProvider class, creating a public/private key pair, and saves the public key information to an RSAParameters structure.